Tor: How to Be Anonymous on the Internet
Tor, the Onion Router, anonymizes your Internet activities by disguising your identity and activity from Internet surveillance in its many forms, as well as helps you bypass Internet filters. The latter come in a large variety of forms – some filters block particular websites based on their IP addresses while others block domain names on search engines.
Tor enables users to conceal their online identity from websites they visit; mask their online destinations from Internet service providers and surveillance techniques; bypass Internet filtering technologies and censorship.
Engineered by a nonprofit group, the Tor Project, Tor has been adopted by liberty advocates and criminals alike. Besides facilitating anonymous communication online, it also gives access to the deep web, the untamed and wild areas of the Internet that are internationally concealed - they never show up on Google’s search results. Being one of the most effective means of defeating online surveillance from intelligence agencies globally, including the NSA spying techniques, ironically, Tor was initially a U.S. governmental project created to secure military communication of the American intelligence.
Benefits
Tor masks your identity and your online activity, allowing you to circumvent censorship and location-specific and electronic restrictions that your government may incur on your country. It is widely used by journalists and freedom activists all over the world.
Tor routes your communication through a distributed network of servers that are located all around the world and monitored by volunteers. In fact, when you connect to it, you become a part of this network, helping anonymize your own activity and provide the anonymity of other users. The nature of Tor prevents anyone surveilling your Internet connection from finding out which websites you visit, as well as it prevents the websites you visit from tracing your physical location.
As far as Tor administrators are concerned, someone may know the fact that you are using the Tor browser, while someone else may know that someone accessed the websites you visited, but nobody will know both.
Tor conceals the fact that you are attempting to connect to specific online resources, but you must keep in mind that it does not conceal the content of your online communication. It is a great layer of protection when you try to access encrypted mail services like RiseUp or Gmail, but unsecured email providers that do not encrypt communication should not be accessed via Tor. Generally, keep in mind that any website sending or receiving content over unsecured http connection leaves your online content exposed.
Basic usage guidelines
Installation Requirements:
Internet connection.
Price:
Free, open source software.
Compatibility:
Tor client is available for Microsoft Windows, Mac, GNU Linux operating systems.
Download:
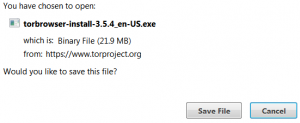
Go to Tor website to download the latest version of the Tor browser Bundle for your OS.
Save the executable file and double-click it when download is completed. Once the Tor browser is extracted, you may delete the executable file.
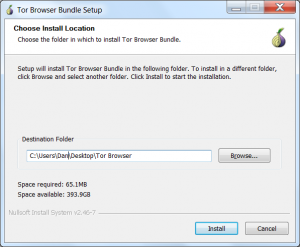
Tor is a Firefox clone, and installation is straightforward - you just extract it by double-clicking on the .exe file. After you choose the language of the program, you will need to choose the location where the bundle extracts.
It does not automatically install in C:\Program Files, but by default it will create a folder on your desktop. Alternatively, you can choose another destination folder on your computer or USB stick (which will effectively help you hide the fact you’re using the Tor).
Once the installation is complete, you can choose to run the browser automatically. From now on, whenever you need to use the Tor browser, go to the Tor Browser folder and double click the Start Tor Browser.exe file to launch the browser.
Accessing Internet
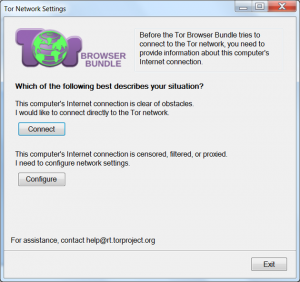
Tor will ask you whether you would like to access the Internet via direct access or restricted access the first time you launch it. Direct access should be used if Tor is not banned in your country while restricted access should be selected if Internet access is restricted or if Tor usage in your country is banned or monitored. We shall default to the basics and take a look at the first option, direct access, but if you would like to know more about how to access Internet using Tor via restricted access, you can take a look at this detailed tutorial.
Either way, you can change the settings any time later from Tor Browser Bundle. When you launch Start Tor browser.exe and see the prompt screen and choose direct access, you will see the next window displaying status window, which shows how Tor connects to the Internet via Tor network.
Seconds later, you will see the browser window that should look like this:
Now you can browse the Internet anonymously.
Using the browser bundle
Being a modified version of Firefox, Tor is very intuitive and easy-to-use for beginners, and at the same time, it allows complex configuration options to advanced users.
Keep in mind that since this browser was designed to protect your privacy and security, it will not save any information about your browsing history on your hard drive or USB dongle. The moment you quit the browser, all your browsing history is deleted.
Important notice: circumvention software like Tor needs to be regularly checked to ensure it works. In order to protect yourself, you need to run independent tests of your Tor browser using the websites that identify your IP. For example, you can use these: check.torproject.org, iplocation.net, ip2location.com, whatismyipaddress.com.
When Tor is fully functional, your location and IP address should be different from the physical location and the actual IP address. From time to time, Tor will prompt you to update its version to the latest available for greater security - every time you launch the browser, it will automatically check for updates and will notify you if a newer version is available for download.
Creating a new identity
It is important you understand that if you like your separate online accounts to be truly anonymous, you need to use different online identities when you access those online accounts such as email clients and social networks accounts.
Tor allows you to create a new identity without resetting your browser and modem. Tor will create a new set of random proxy servers, which will make you appear like someone else from a totally different location. To create a new identity in Tor, click on the onion icon at the upper left corner of your browser and choose New identity from the drop-down menu.
The browser will close, eliminate your browsing history and cookies, and restart itself. Once the browser starts again, you can verify your new location to make sure you are using a completely new identity.
NoScript Add-on
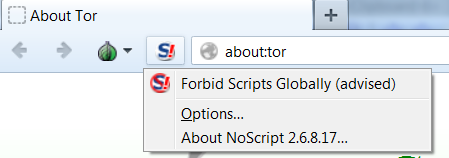
Tor browser comes with NoScript preinstalled but it is not activated by default, so if you want that extra layer of protection against malicious scripts execution, you can enable the NoScript add-on by opening the NoScript menu -> Forbid scripts globally.
Additionally, you could run Tor sandboxed in Sandboxie.
One more important thing you need to understand when using Tor is other programs on your computer communicate with Internet not using Tor - they access the Internet directly.
The Tor Project website offers extensive tutorials and manuals on tweaking the browser to fit the needs of the most advanced users, but if you have any questions, we will be glad to assist you in sorting things out.
Sources: the Tor Project, Security in a Box.